Evgeny Gaevoy, CEO of Wintermute, has provided a candid assessment of the current situation of the decentralized finance sector, highlighting the structural risks that continue to hinder innovation.
DeFi is not doing well
Gaevoy expressed concerns about the ability to compound and how interconnected protocols increase risk rather than distribute it, saying that things are looking pretty bleak for DeFi innovation at this stage, in response to recent developments.
His argument is based on a fundamental principle of DeFi. Protocols can build on each other thanks to the ability to compose, which is often touted as one of the industry’s biggest advantages. In reality, the same characteristic produces tightly coupled systems in which a single fault can propagate to multiple layers.
According to Gaevoy, the way to assess risk has changed since the spillover effects of exploits are no longer captured in a single protocol.
Series of attacks
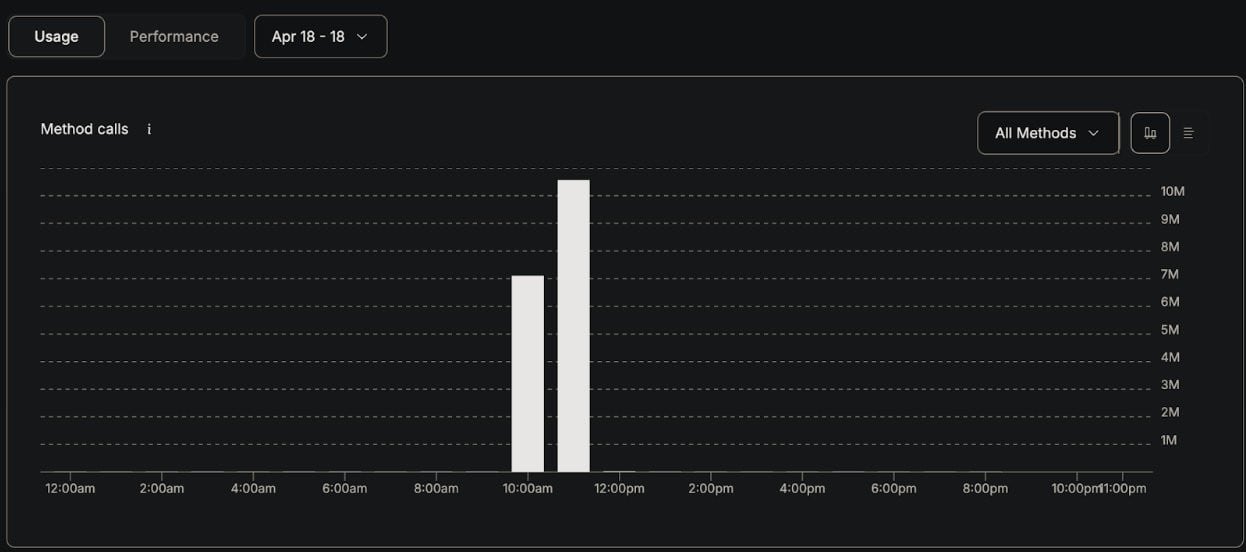
His comments come at an opportune time. On April 18, 2026, KelpDAO was the victim of an exploit worth approximately $290 million. Early signs point to a highly skilled state-affiliated actor, most likely linked to the DPRK’s Lazarus Group.
The attack itself was not a simple smart contract glitch. Instead, it specifically poisoned downstream RPC nodes used in the LayerZero Labs Decentralized Verifier Network. Under very specific circumstances, this allowed attackers to change authentication paths.
What matters in the bigger picture is how the system design influenced the outcome. Due to a 1-to-1 DVN configuration, the incident was limited to KelpDAO’s rsETH configuration, creating a single point of failure. Although explicitly supported by LayerZero’s architecture, multi-DVN configurations with redundancy are not implemented.
As a result, once the attack path was established, there was no independent validation layer to reject spoofed messages.
The event strengthens Gaevoy’s position, despite the technical containment and lack of contamination with other assets or applications. The complexity required to secure interconnected systems continues to grow, even if damage remains limited. With each new integration, the attack surface grows, and highly skilled actors are starting to take advantage.

