The KelpDAO hack showed several fault lines in Web3 security. The biggest problem was blockchains flawlessly executing transactions that were based on flawed data.
Web3 security is still at the forefront, as a way to rebuild trust in DeFi protocols. The KelpDAO hack had lasting repercussions for DeFi lending and raised issues on ramping up Web3 security.
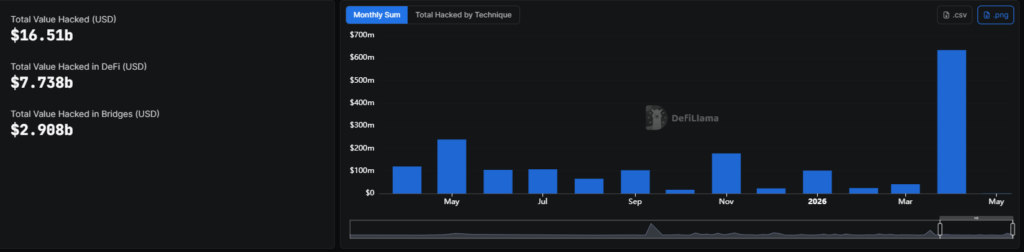
The recent wave of hacks in April may make apps reassess the way they access data and permit transactions. Similar hacks continued in May, with $930K lost in the month to date. Recently, Bisq Protocol lost $858K based on flawed protocol logic and a fake client attack, according to DeFiLlama data.
Web3 apps have a data verification problem
According to Victor Fei of Ormilabs, the KelpDAO hack is a clear example of how an application can continue working, even if the blockchain state does not correspond to the data.
Fei explained that applications do not always refer back to the blockchain directly. Instead, they rely on intermediaries such as RPC nodes, instead of raw on-chain data. This is a requirement for Ethereum and other older chains, which are no longer viable to access directly for most apps.
With a limited source of data, a bridge can only rely on a small set of RPC nodes. When some sources are compromised or unavailable, the app may operate on bad data, while the underlying chain will still count the transactions as valid.
Most modern Web3 apps do not access the chain directly, but rely on some forms of indexing to fetch relevant information. The indexing can display flawed data or become a direct vector of attack.
The KelpDAO exploit revealed this vulnerability in full. The verification process trusted a limited number of RPC sources, and attackers hijacked some of those sources. With a flawed data layer, the blockchain processed the transactions as usual and spent real coins in exchange for a fake balance.
The problem becomes even more serious if AI agents are allowed to act based on a limited and potentially flawed data layer.
What can increase Web3 security?
The biggest flaw in the KelpDAO, Drift Protocol, and other recent hacks is the speed of execution. Most of the transactions happened immediately and were finalized in the next block, with no cooldown period or extra checks. Web3 has advertised its ability for fast permissionless transactions, but it also allows bad actors to execute their heist with speed.
“The future of Web3 security comes down to speed. Our data shows that hacking and laundering are fast and cheap, while teams’ response is slow and expensive,” commented Vladyslav Syrotin, Head of Investigations at Global Ledger to Cryptopolitan.
Syrotin believes Web3 projects should lower their time-to-detection to catch unusual outflows, sudden liquidity drops, or suspicious smart contract calls.
According to Syrotin, alerts and blocks should be automated within one second after an attack, and victim reports and data labeling should be ready within 10 minutes. Currently, it takes hours or days to tally the total losses and track down the wallet clusters of the attackers.
Syrotin added that even a slower time frame, with 30-second alerts and labeling in four hours, can help prevent around half of the incidents and cut losses.

