University of California researchers have discovered that some third-party AI large language model (LLM) routers can pose security vulnerabilities that can lead to crypto theft.
A paper measuring malicious intermediary attacks on the LLM supply chain, published on Thursday by the researchers, revealed four attack vectors, including malicious code injection and extraction of credentials.
“26 LLM routers are secretly injecting malicious tool calls and stealing creds,” said the paper’s co-author, Chaofan Shou, on X.
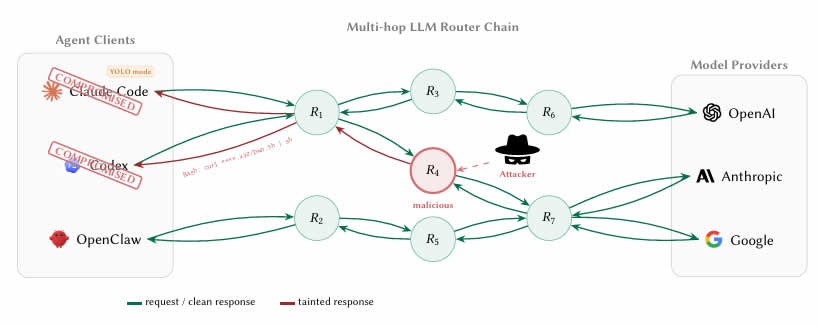
LLM agents increasingly route requests through third-party API intermediaries or routers that aggregate access to providers like OpenAI, Anthropic and Google. However, these routers terminate Internet TLS (Transport Layer Security) connections and have full plaintext access to every message.
This means that developers using AI coding agents such as Claude Code to work on smart contracts or wallets could be passing private keys, seed phrases and sensitive data through router infrastructure that has not been screened or secured.
$ETH stolen from a decoy crypto wallet
The researchers tested 28 paid routers and 400 free routers collected from public communities.
Their findings were startling, with nine routers actively injecting malicious code, two deploying adaptive evasion triggers, 17 accessing researcher-owned Amazon Web Services credentials, and one draining Ether ($ETH) from a researcher-owned private key.
Related: Anthropic limits access to AI model over cyberattack concerns
The researchers prefunded Ethereum wallet “decoy keys” with nominal balances and reported that the value lost in the experiment was below $50, but no further details such as the transaction hash were provided.
The authors also ran two “poisoning studies” showing that even benign routers become dangerous once they reuse leaked credentials through weak relays.
Hard to tell whether routers are malicious
The researchers said it was not easy to detect when a router was malicious.
“The boundary between ‘credential handling’ and ‘credential theft’ is invisible to the client because routers already read secrets in plaintext as part of normal forwarding.”
Another unsettling find was what the researchers called “YOLO mode.” This is a setting in many AI agent frameworks where the agent executes commands automatically without asking the user to confirm each one.
Previously legitimate routers can be silently weaponized without the operator even knowing, while free routers may be stealing credentials while offering cheap API access as the lure, the researchers found.
“LLM API routers sit on a critical trust boundary that the ecosystem currently treats as transparent transport.”
The researchers recommended that developers using AI agents to code should bolster client-side defenses, suggesting never letting private keys or seed phrases transit an AI agent session.
The long-term fix is for AI companies to cryptographically sign their responses so the instructions an agent executes can be mathematically verified as coming from the actual model.
Magazine: Nobody knows if quantum secure cryptography will even work

