The hack of the Solana-based decentralized finance (DeFi) platform Drift Protocol could have been prevented if standard operational security procedures were followed by the Drift team, and may constitute “civil negligence,” according to attorney Ariel Givner.
“In plain terms, civil negligence means they failed their basic duty to protect the money they were managing,” Givner said in response to the post-mortem update provided by the Drift team and how it handled Wednesday’s $280 million exploit.
The Drift team failed to follow “basic” security procedures, including keeping signing keys on separate, “air-gapped” systems that are never used for developer work, and conducting due diligence on blockchain developers met through industry conferences.
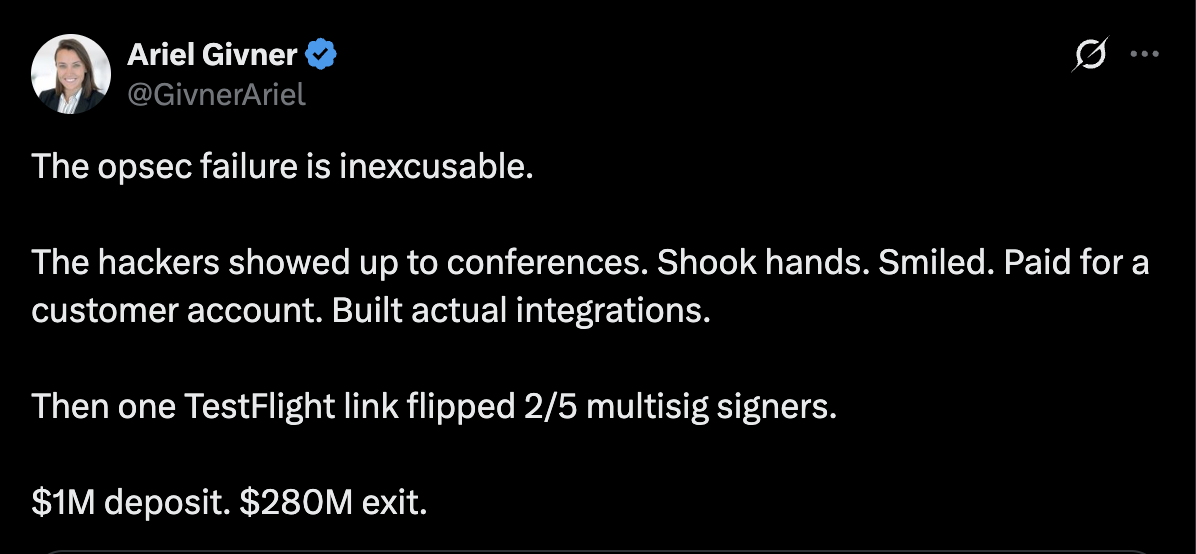
“Every serious project knows this. Drift didn’t follow it,” she said, adding, “They knew crypto is full of hackers, especially North Korean state teams.” Givner continued:
“Yet their team spent months chatting on Telegram, meeting strangers at conferences, opening sketchy code repos, and downloading fake apps on devices tied to multisignature controls.”
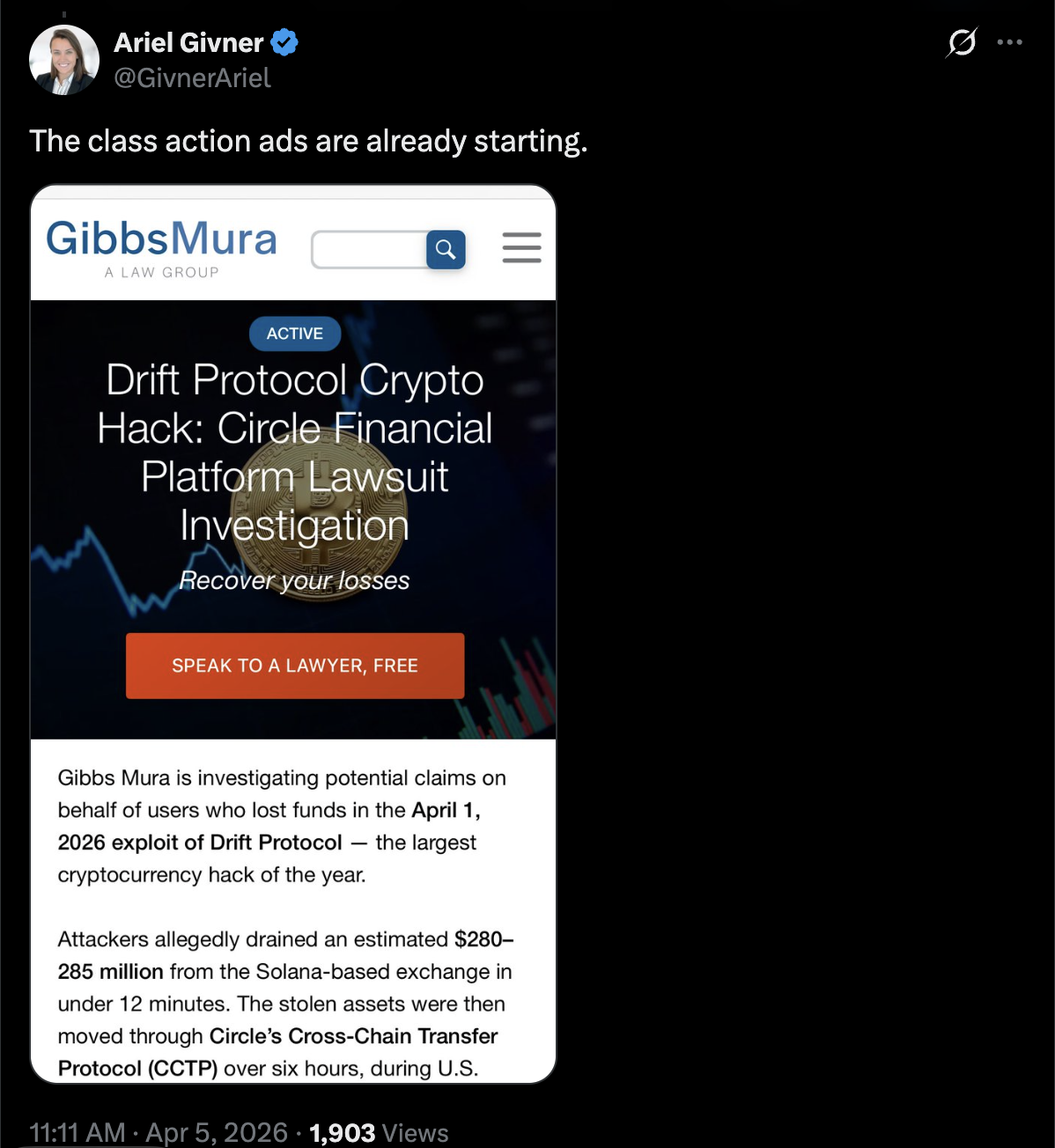
Advertisements for class action lawsuits against Drift Protocol are already circulating, she said. Cointelegraph reached out to the Drift Team but did not receive a response by the time of publication.
The incident is a reminder that social engineering and project infiltration by malicious actors are major attack vectors for cryptocurrency developers that could drain user funds and permanently erode customer trust in compromised platforms.
Related: Drift explains $280M exploit as critics question Circle over USDC freeze
Drift Protocol says attack took “months” of planning
The Drift Protocol team published an update on Saturday outlining how the exploit occurred and claimed that the attackers planned the attack for six months before execution.
Threat actors first approached the Drift team at a “major” crypto industry conference in October 2025, expressing interest in protocol integrations and collaboration.
The malicious actors continued to build rapport with the Drift development team in the ensuing six months, and once enough trust was built, they began sending the Drift team malicious links and embedding malware that compromised developer machines.
These individuals, who are suspected of working for North Korea state-affiliated hackers and physically approached the Drift developers, were not North Korean nationals, according to the Drift team.
Drift said, with “medium-high confidence,” that the exploit was carried out by the same actors behind the October 2024 Radiant Capital hack.
In December 2024, Radiant Capital said the exploit was carried out through malware sent via Telegram from a North Korea-aligned hacker posing as an ex-contractor.
Magazine: Meet the hackers who can help get your crypto life savings back