Resolv Labs acted on Sunday to reassure users after an exploit hit the issuance mechanisms of its USR stablecoin, knocking the token off its dollar peg and prompting decentralized finance (DeFi) protocols with exposure to act quickly to limit any fallout.
Cointelegraph reported earlier Sunday that an attacker abused USR’s coin mechanisms, creating tens of millions of unbacked tokens and dumping them through DeFi pools, breaking the stablecoin’s peg and prompting Resolv to pause protocol functions while it assessed the damage.
The token fell to $0.14 after the exploit (86% below its target price of $1) before returning to $0.42 at the time of writing, according to data from CoinGecko.
In a recent statement on The containment and impact assessment remains ongoing.
Onchain data from Arkham, confirmed by Web3 security firm Cyvers, showed that the attacker had converted most of the minted USR into Ether ($ETH), with some of the loot being sold for around 11,400 $ETH (about $24 million). Independent analysts also noted that the remaining USR 36.74 million “was still being dumped continuously.”
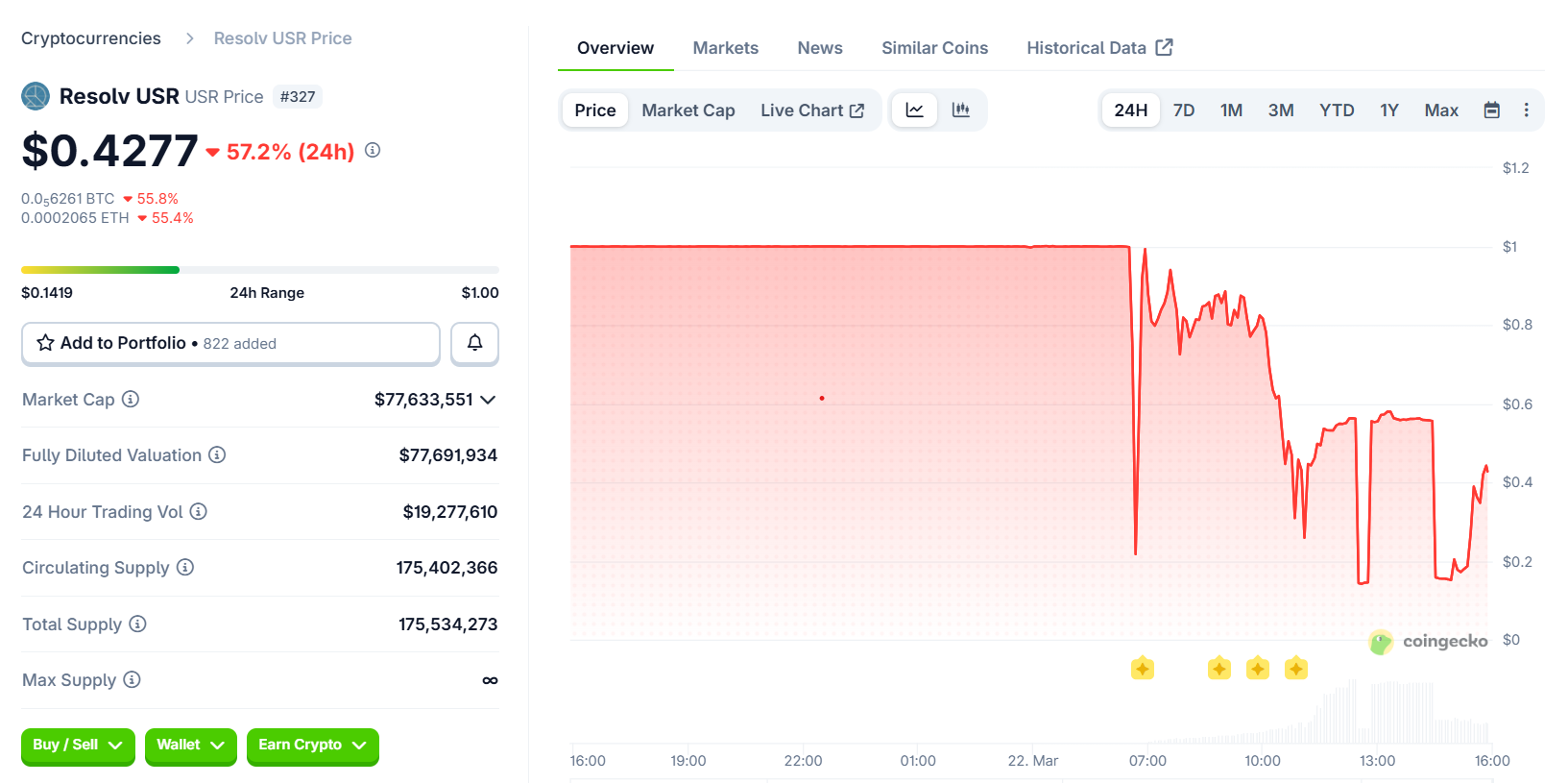
USR fell 86% from its fixed value. Source. Coin gecko
Michael Pearl, vice president of GTM and strategy at Cyvers, told Cointelegraph that since the supply had blown up faster than the market could absorb and the token was immediately delinked, the value of the remaining tokens had been significantly eroded.
Related: Google threat Intel signals crypto-stealing malware ‘Ghostblade’
DeFi protocols try to limit the consequences
Decentralized finance (DeFi) protocols with exposure to Resolv rushed to clarify their positions. Liquid staking provider Lido said Lido Earn user funds were safe. Merlin Egalite, co-founder of Morpho, emphasized that the lending protocol’s own contracts were not affected and that only certain vaults had exposure, and Aave founder Stani Kulechov said that the platform had no direct USR exposure and that Resolv was paying down its outstanding debts.
The “yieldsandmore”
Pearl told Cointelegraph that, based on available data, exposure appeared to be “relatively concentrated” in the credit markets and leverage loops “rather than system-wide,” and particularly in protocols that integrated USR, wstUSR or RLP into credit, leverage or return strategies.
Related: Hacked crypto tokens drop by 61% on average and rarely recover, the Immunefi report said
He said several protocols, such as Euler, Venus, Lista and Fluid, had taken precautions such as pausing markets or isolating vaults, while other protocols had declared no exposure at all. “It is more accurate to describe the risk as concentrated with local spillovers, rather than widespread contagion,” he said.
Ledger Technical Director Charles Guillemet also assessed the implications of
Questions surrounding the limitations of security audits
Resolv’s smart contracts have undergone multiple audits since 2024, but Pearl said that while audits were “necessary”, they were also “inherently static and scoped”. Real-time, artificial intelligence-powered monitoring to “continually analyze protocol activity” was necessary, he argued, to detect anomalies as they occur.
Specific to stablecoin systems, he said, this meant monitoring mint and burn flows against expected behavior in real time, continuously validating supply against reserves and supporting assets, and detecting anomalies in oracle inputs, pricing and liquidity conditions.
Security firm Pashov, which audited Resolv’s staking module in July 2025, told Cointelegraph that Resolv’s design was “good” and that the root cause was “not so much the design, but rather the compromise of the private key,” which was likely an operational security flaw. “We need to understand why that happens,” he said.
Cointelegraph contacted Resolv Labs for comment but had not received a response by publication.
AI eye: IronClaw competes with OpenClaw, Olas launches bots for Polymarket

