In an alert shared by Project 0 (P0) founder MacBrennan Peet, the executive committed to fully refund confirmed losses after attackers infiltrated its system to redirect user visits to its website to a crypto-stealing site.
The post by MacBrennan confirmed that at least one user lost $1,000 when they tried the new site “out of curiosity.”
The security incident targeting Project 0 compounds record numbers of crypto thefts by bad actors exploiting the Fusaka upgrade that was supposed to make transaction fees an afterthought for Ethereum network users, adding to a pattern of attacks targeting liquidity-rich venues.
Project 0 reports the latest DeFi domain hijack
According to the disclosure by MacBrennan, attackers gained access to the GitHub account of an application team member, which allowed them to redirect user visits between 9:45 PM and 10:19 PM.
Although he did not specify his timezone, users who tried to visit Project 0’s website within the 40-minute attack window were directed to another website that led to the loss of at least $1,000.
Per Defillama data, Project 0, a DeFi-native prime brokerage that lets users borrow against their entire DeFi portfolio across multiple venues, currently holds almost $90 million in total value locked (TVL), peaking above $110 million since tracking began in late 2025. The project also claims backing by Multicoin, Pantera and Solana Ventures.
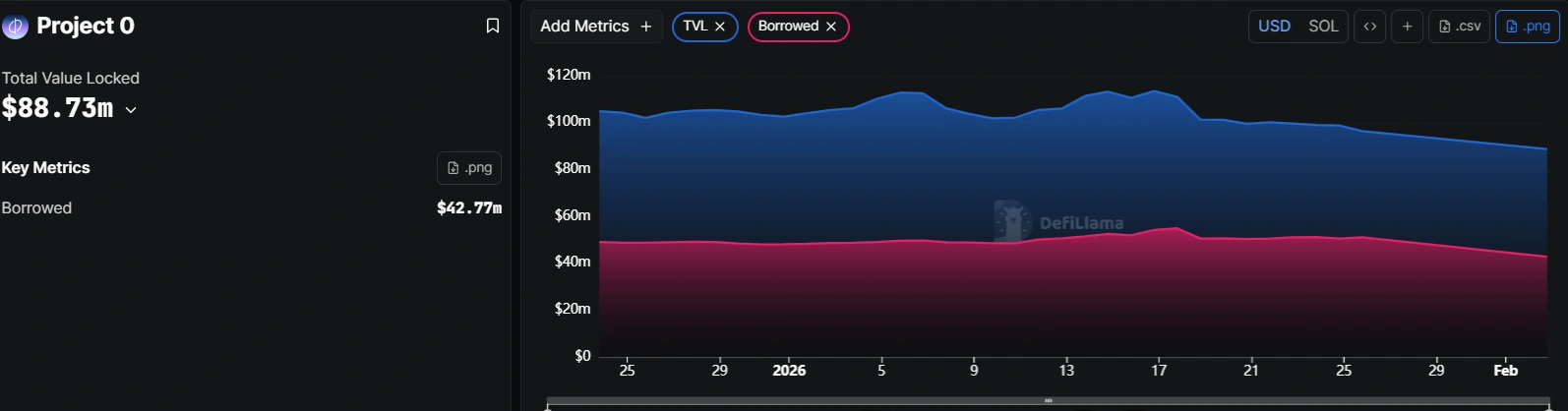
The $89 million locked in Project 0’s DeFi ecosystem was unaffected by the exploit. Source: Defillama
That level of activity and status, while attractive to users, is also a beacon for attackers looking for high-value targets.
See also Slavi Coin: Slavi Kutchoukov announces the launch of his crypto
Cryptopolitan reported that OpenEden and BonkFun endured similar attacks when attackers compromised domains registered to the projects.
In both cases, the attack did not affect project vaults or users’ positions, as the damage in these kinds of attacks is typically limited to website visitors during the exploit window, which is usually quickly mitigated by responsive teams.
While the exact amount lost is still unconfirmed, MacBrennan has committed to extending refund relief to any other verified customer losses during the attack.
Ethereum users become targets of address poisoning attacks
When Ethereum developers pushed through the Fusaka upgrade in December 2025, they touted the upgrade as the “final boss” in making mainnet transactions affordable.
What they did not see coming was that it would become the final puzzle piece for attackers stalking high-value targets in the liquidity-rich Ethereum ecosystem, which holds almost $60 billion across DeFi protocols and over $160 billion in stablecoin market cap.
The official Etherscan account on X called out the growing menace in its “Address Poisoning Attacks Are Rising on Ethereum” article. The report cited a 2025 study comparing poisoning attempts before and after the Fusaka upgrade to highlight the proliferation of these attacks since the December upgrade.
Dust transfers, which are small deposits (below $0.01) meant to replace addresses in users’ transaction history with wallets controlled by the attackers, followed the trend as transaction activity on the Ethereum mainnet increased about 30% across the board in the 90 days following the Fusaka upgrade, with an accompanyong 78% increase in new address creations.
See also Amercian authorities seek to extradite Swedish citizen from Thailand in 11m dollars case
Table comparing the rate of address poisoning attacks before and after the Fusaka upgrade.
It’s a numbers game
Cryptopoitan has reported several high-profile losses to the new bane of Ethereum users, with the $50 million loss from December creating the biggest headline. Apparently, the victim in the incident actually sent $50 in a test transaction to be sure they had the correct address.
However, in the time it took to test the address and initiate the actual $50 million transfer, bad actors had punctuated the sender’s transaction history with their own dust transfers, which ultimately led to the loss.
That incident highlights the scale and speed of these operations, as attackers actually compete to out-poison potential victims’ addresses. As Etherscan highlighted, “just two stablecoin transfers” by a user of its service triggered “more than 89 address watch alert emails.”
Only about 1 in 10,000 attempts are successful, but when one compares the $79 million in confirmed losses across 17 million attempts targeting about 1.3 million users, the math adds up for these attackers, who incur less than $1 on each attempt.